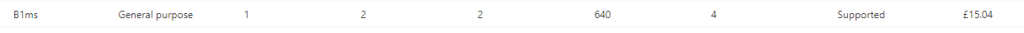
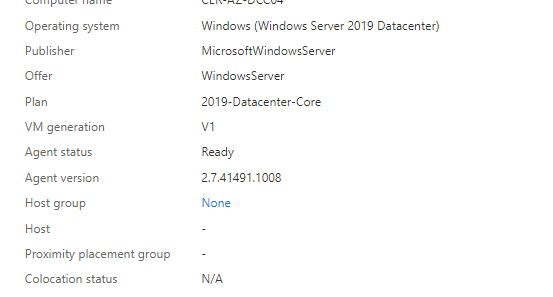
Firstly well look at the specs that in this case I have used for this matter
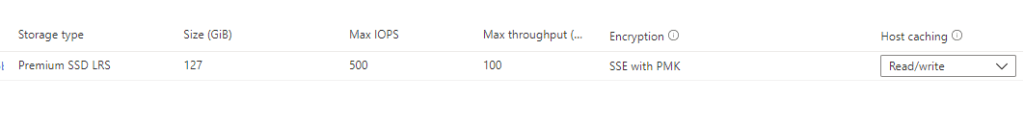
In this case since is a Core server we selected B1mS with premium SSD
Ensure you patch the server using Sconfig. Beforehand raising it as a Domain controller .
Recommended 0 trust config NSGS ( only for AD , it comes with Remote desktop disabled so you open it when needed to interact from the server) Seven IT recommends that you use a PAW or jump server to connect to AD from a vpn network for security reasons . If you are unsure how to understand this part skip it.
This NSG config will leave the server not contactable as you can see we block RDP in rule 105
You must open RDP if you wish to make changes , This is just for security model 0 trust
105: Blocks RDP from any source
200: TCP AD ports
201: UDP AD ports
202:TCP/UDP ( ephemeral ports )
500: Deny all rest of traffic
Inbound
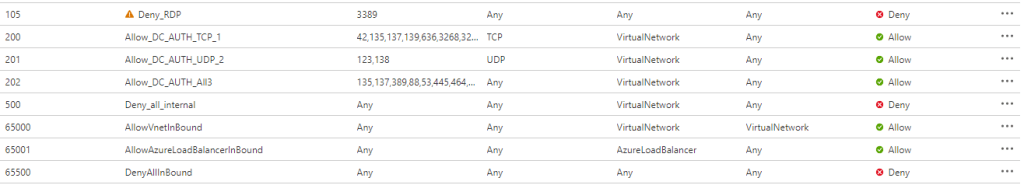
Breakdown of Inbound ports

Raising the domain controller
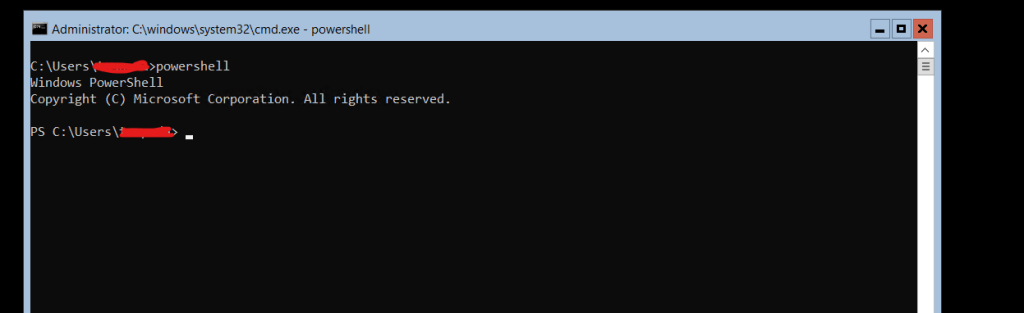
1.Load PowerShell
2.
Run
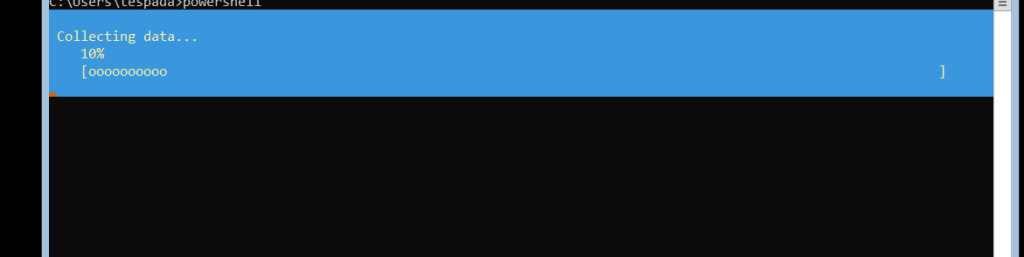
Install-WindowsFeature -Name AD-Domain-Services -IncludeManagementTools
As per azure specs if you have configured the DNS in the Network you don’t need to change anything in the network cards so we will raise the DC with the following command:
Where your domain name = domain name + user
Install-ADDSDomainController -InstallDns -Credential (Get-Credential <DomainName\Administrator>) -DomainName <DomainName> -SafeModeAdministratorPassword (ConvertTo-SecureString -AsPlainText "<Administrator Password>" -Force)
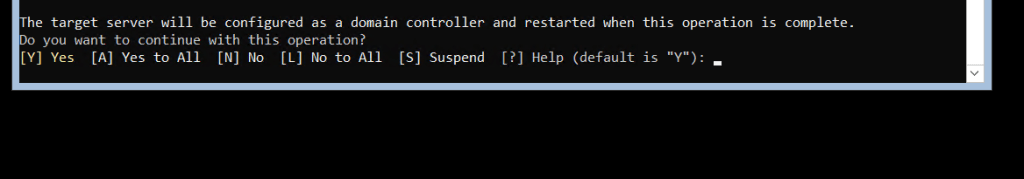
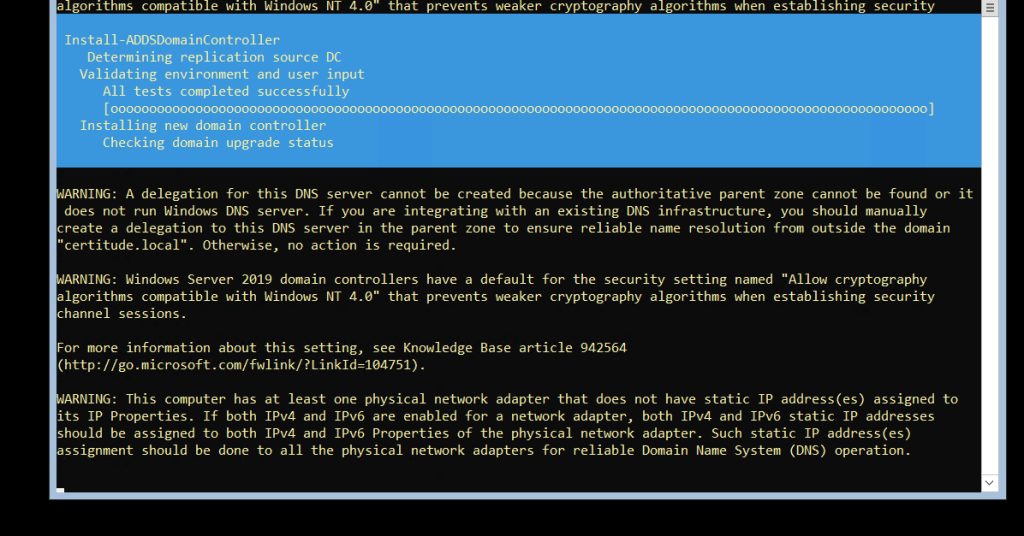
The warnings are completely normal
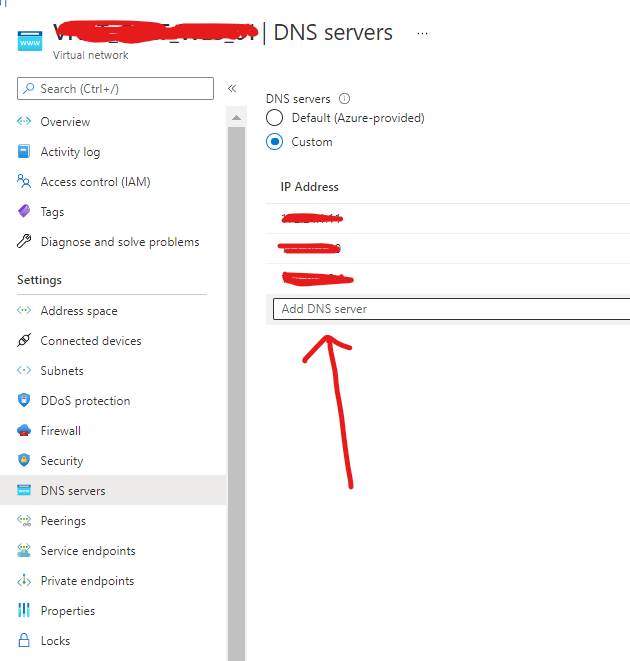
Make sure in Azure you have set STATIC IP on the VM . And that you have configured the dns’s in the Vmnetwork as follows:
If you have to assign a NSG also you can change it here,
VMNET ( adding DNS settings ) . If you using Azure vpn this will cause the clients to disconnect !

Now you should have your new core DC up and running in the azure enviorment.

