The requirements:
- Experience for log analytics and setting up alerts ( the guidance assumes you have configured all the requirements)
- Azure Sentinel integration data sources
- Log Analytics Workspace linked to Sentinel
- Azure Sentinel Alert Rule
- Integration in Analytics workspace of Azure AD, Virtual machine logs for analysis
Usefull Links
https://docs.microsoft.com/en-us/azure/sentinel/quickstart-onboard
https://docs.microsoft.com/en-us/azure/active-directory/reports-monitoring/
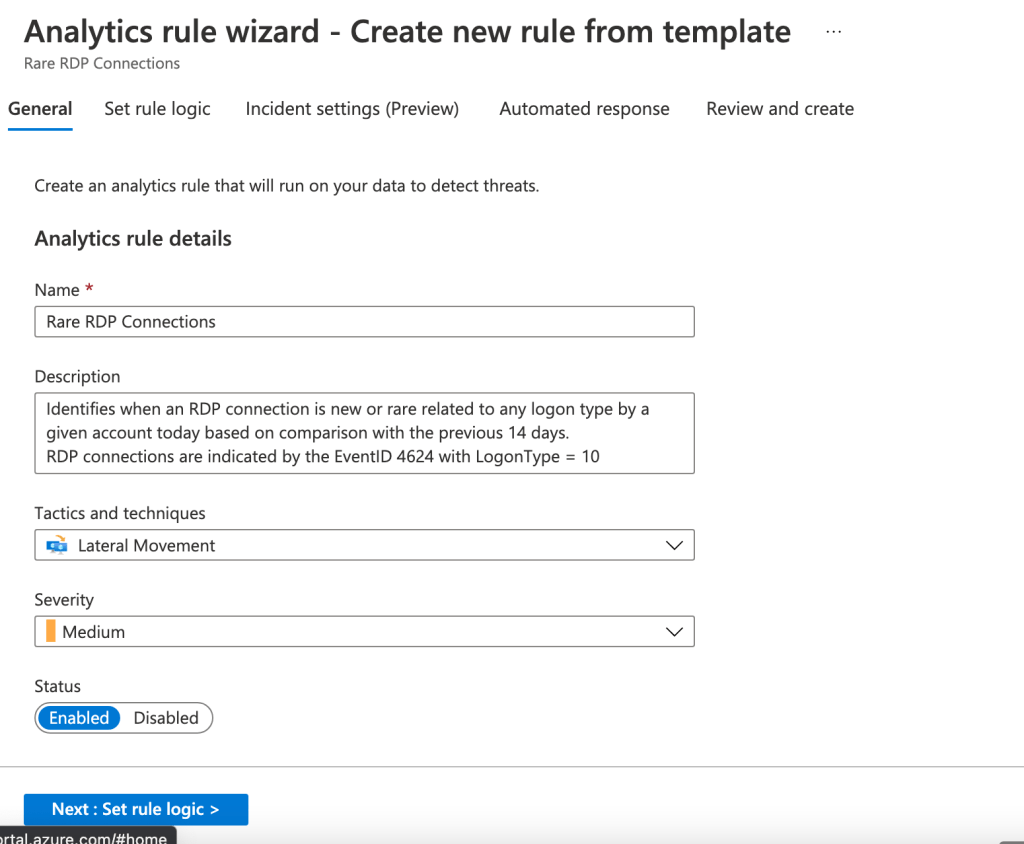
Create the alert rule from analytics in sentinel
Click ont the rule template and hit create
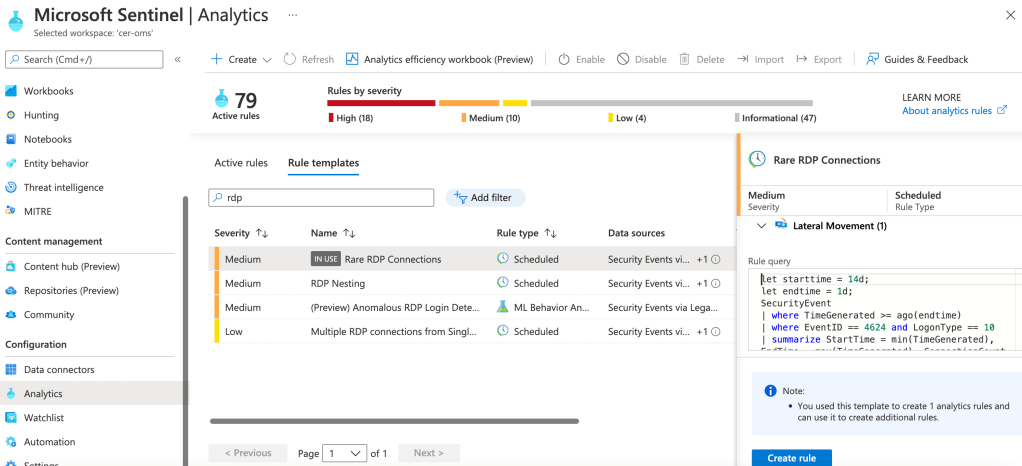
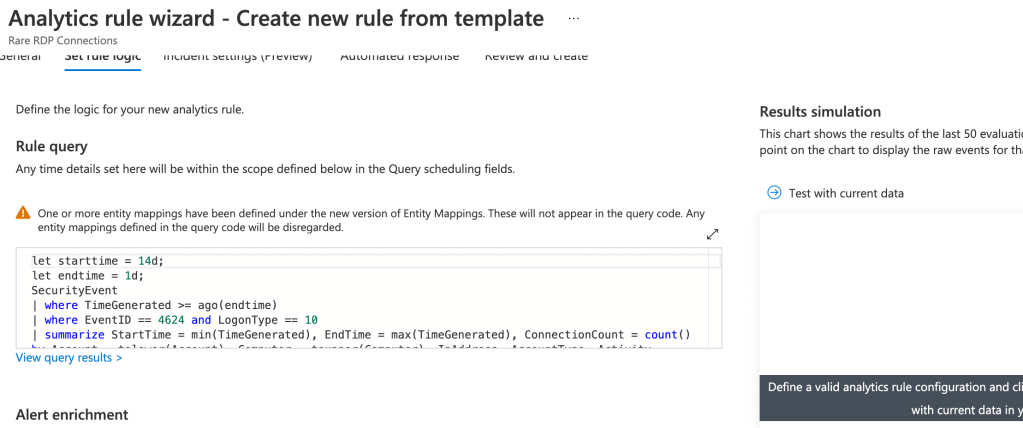
Configure any rule logics and naming conventions
You can also simulate how many alerts the rule would generate when enabled
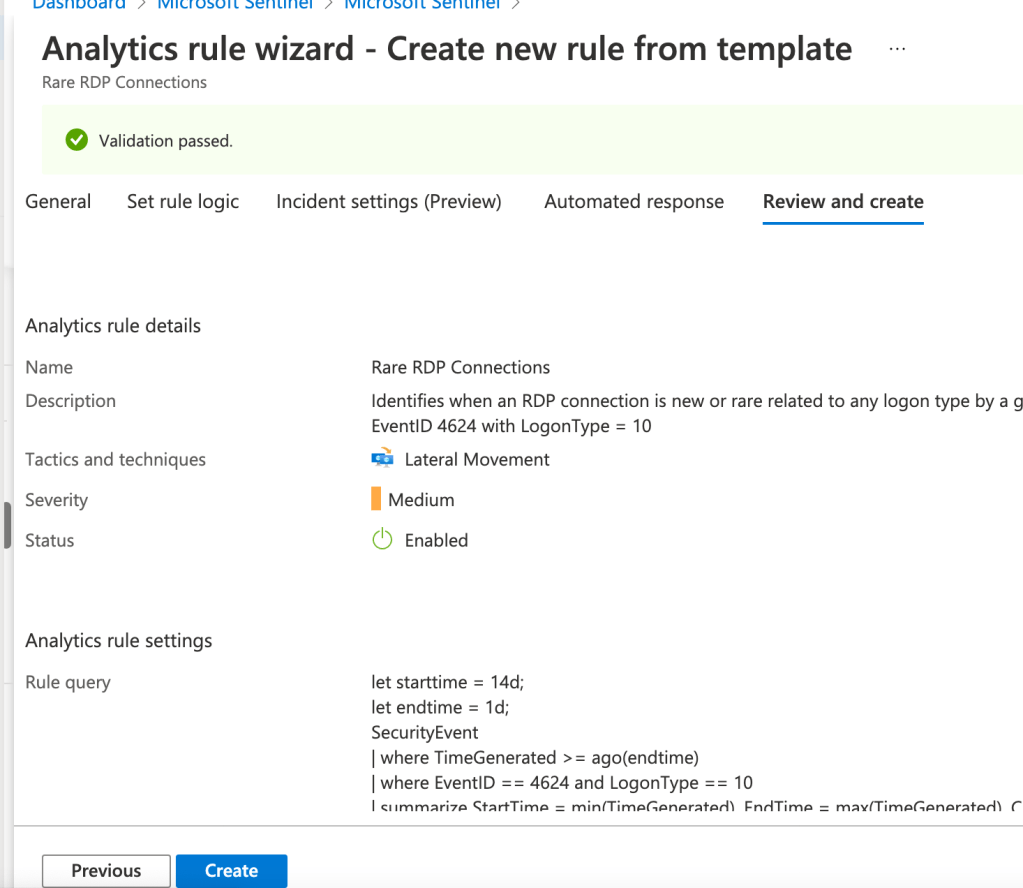
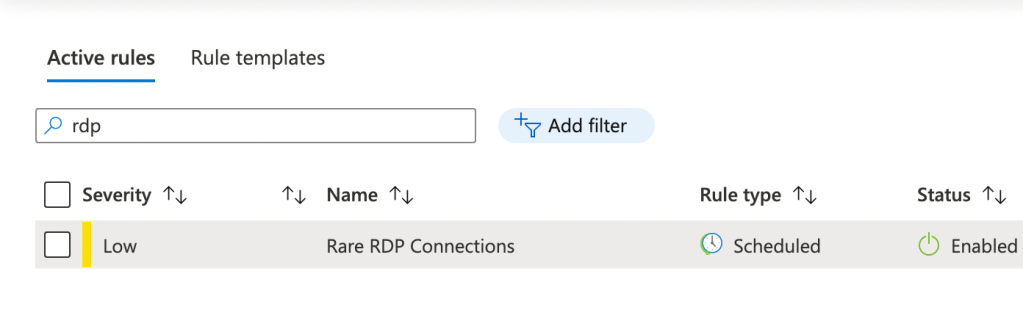
Once the alert is enabled is ready to trigger
Once the alert is configured ( in our case we havea case of an unusual RDP login by a new legit admin in the system , that would be a false positive becase we know is a legit access ). This created an incident in sentinel
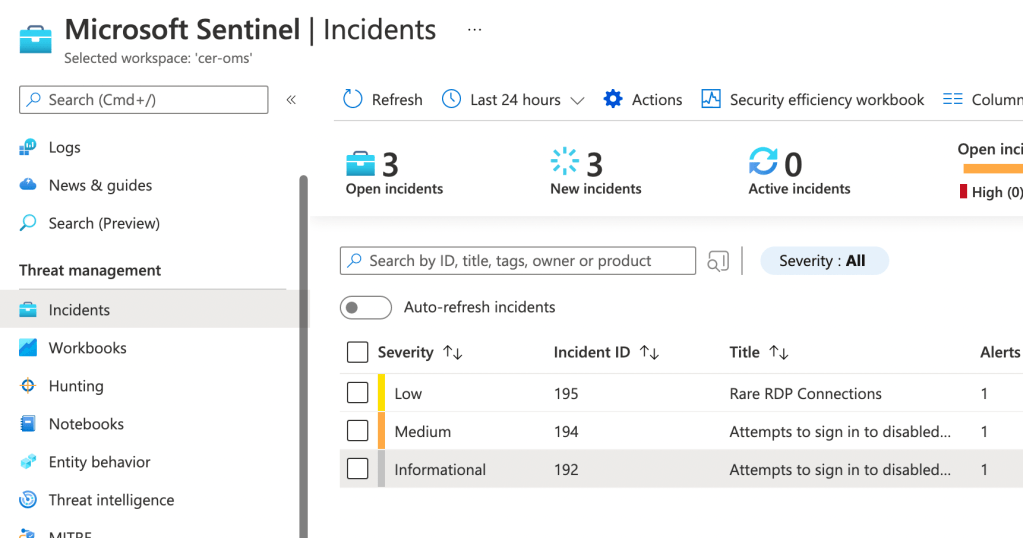
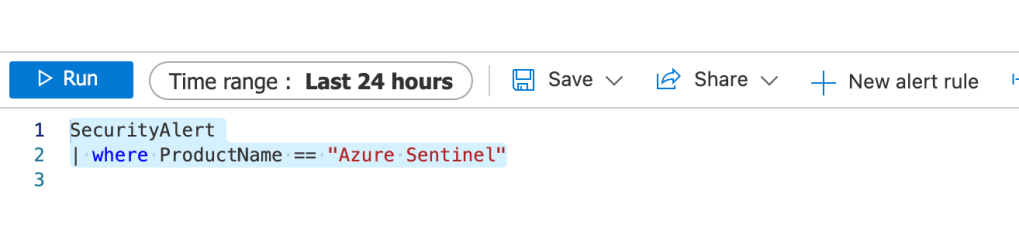
Now here is the trick, if we launch the following query we can see al the Sentinel incidences in the last 7 Days ( log analytics query )
SecurityAlert
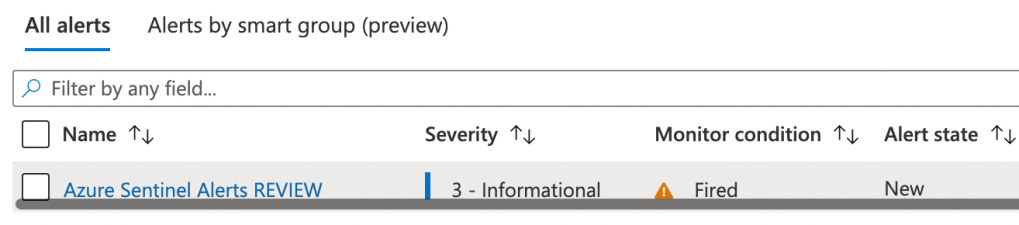
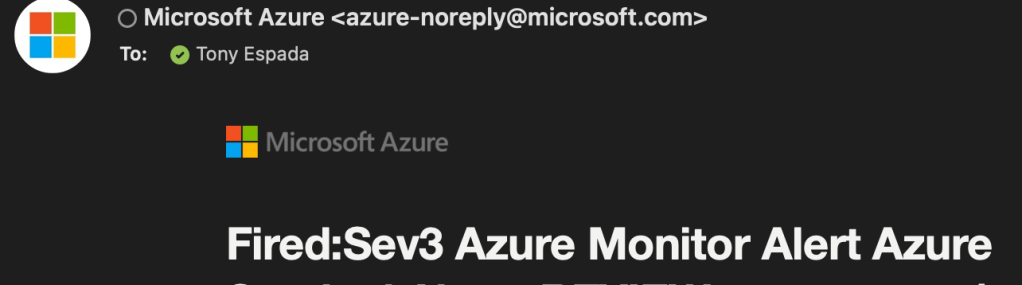
| where ProductName == "Azure Sentinel"We can create now an alert rule to alert us whenever there is alerts, clicking in new alert rule !