PNP PowerShell is a .NET Core 3.1 / .NET Framework 4.6.1 based PowerShell Module providing over 600 cmdlets that work with Microsoft 365 environments such as SharePoint Online, Microsoft Teams, Microsoft Project, Security & Compliance, Azure Active Directory, and more.
Knowing that, what can we do to proactively secure and Monitor this changes
Malicious actions that can be done with PNP on top of my head
- Deletion of Sharepoint Data
- Removal of Version history
- Major changes in configurations on Sites
- Massive Upload
- Other possible disruptive and nasty changes in bulk
- Exfiltration
- Ransom of files
1. First and Foremost. Restrict PNP app in the Azure tenant.
- As proactive practice, just don’t allow users to set permissions in apps in Azure
- Ensure in the blade of Enterprise Applications, Users can add apps is into the option NO.

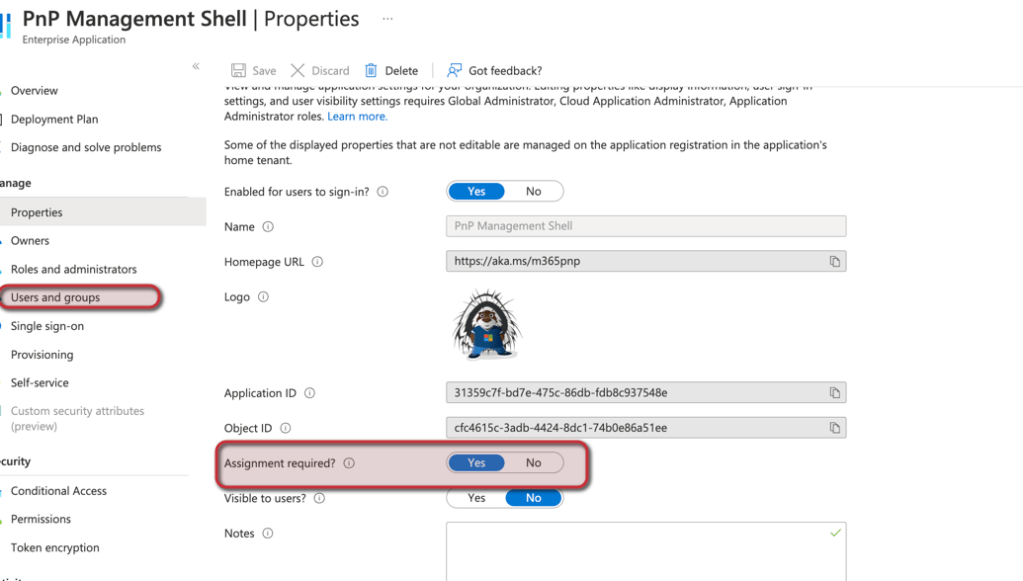
2.PNP needs access to the tenant as app. Ensure only certain users or by default is disabled and on demand via PIM or a security group.
- You can assign the PNP app to a group
- You can make such group to act like a PIM
- Ensure “Assignment is required “to only the users/admins that are to use PNP
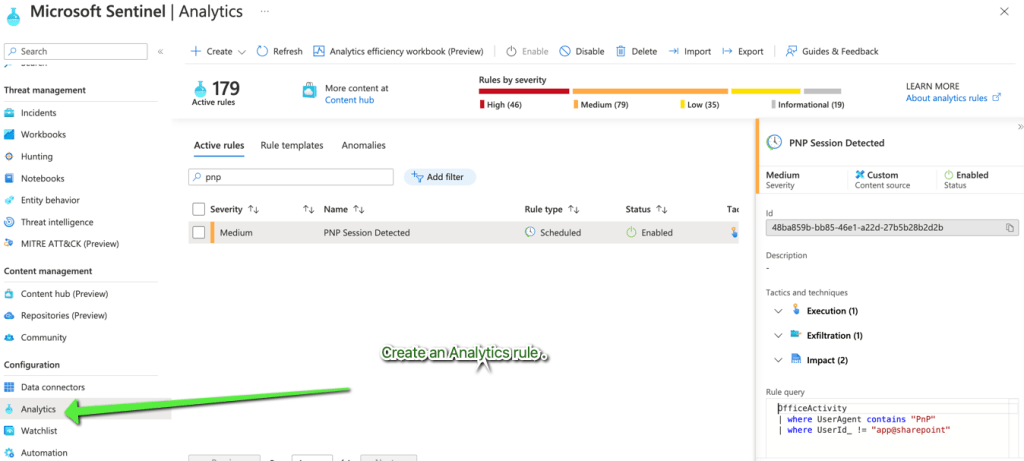
3. Monitor in Sentinel or Other Security tools the access.
- Your Azure logs must be integrated in Log analytics to use with Sentinel
- Use Analytics rule
- Monitor via Log analytics
- You may also create automation (like blocking access) via Sentinel
OfficeActivity
| where UserAgent contains "PnP"
| where UserId_ != "app@sharepoint"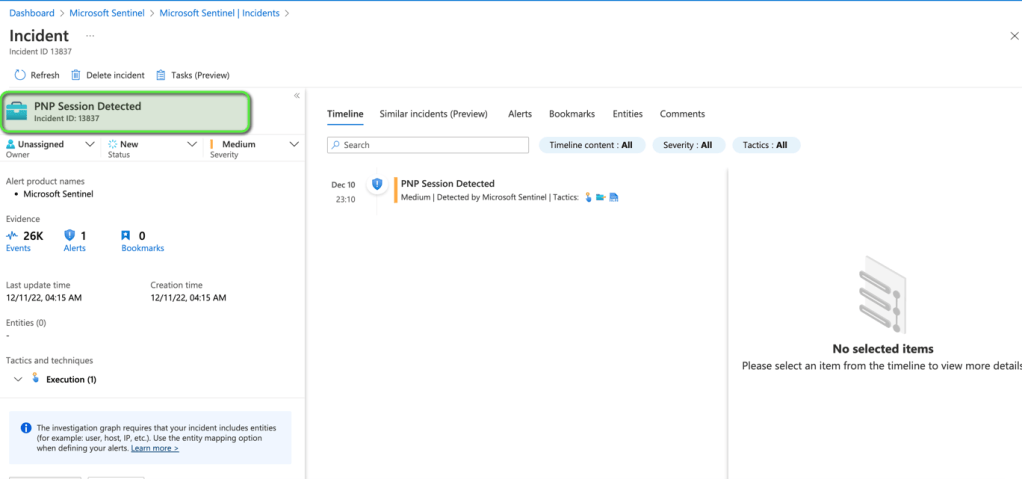
4. The more important Bit: Backup Your environment and use Retention Policies
- It is essential you have an external backup of Sharepoint as Microsoft does not back up your Sharepoint environment
- Use Retention policies in sites where disasters can occur
