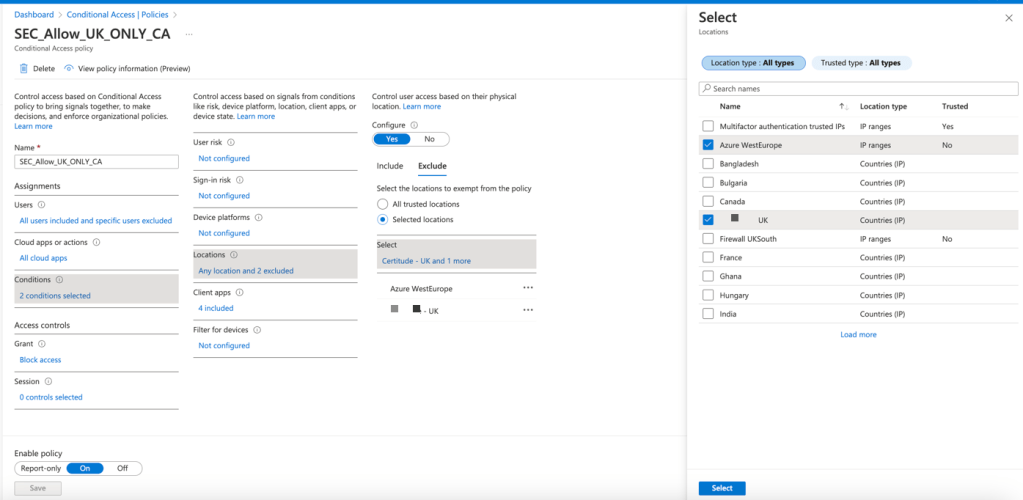
A common way to protect your azure & Office 365 tenant, reducing the exposure, is a conditional policy allowing only to perform logins on the source country of origin. Since there are as many countries as you can guess, the attackers or adversaries will also have to guess such country.
The idea of this monitoring & Automation is to reduce attack surface in case someone could have guessed the password or stolen the auth cookie on one of your users, hence using it from a malicious machine. But adversaries may not know or not be aware of this conditional policy, hence this could be handy to protect the users.
In this case, we are not going to block corporate devices, we understand the majority of this surface attacks or miss use of the users (VPN, travel) comes from personal devices.
Our defences will be the following :
- Combine this automation with MFA Conditional policy
- Combine this automation with Block Legacy AUTH conditional Policy
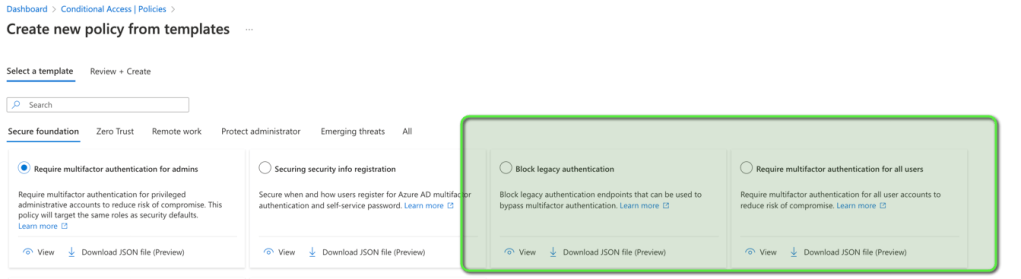
You can apply these policies from the Templates blade.
- Conditional Policy, only allowing Country where the company works or has branches to access
Click here for MS article on how to do this
- Automate successful logins from countries not expected and block personal devices (
- In this case, our country will be GB (Great Britain). As per the Analytics rule on Sentinel.
Automation of successful logins block from unexpected countries
- Step 1 : Create the Sentinel Analytic rule When creating the rule make sure you map entities (account , Full name , User ID )
- Configure the rule to run looking the desired time ( 4h , 1h ) etc. on the logins logs
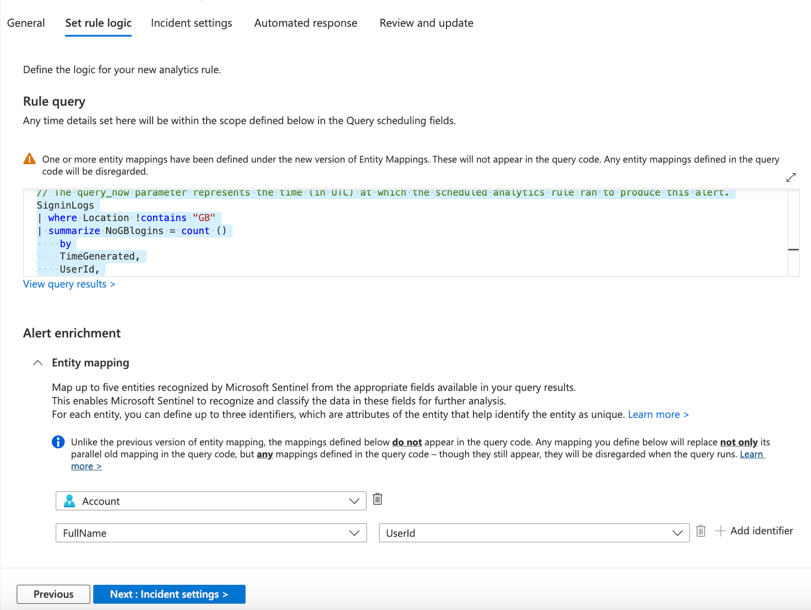
SigninLogs
| where Location !contains "GB"
| summarize NoGBlogins = count ()
by
TimeGenerated,
UserId,
UserDisplayName,
UserPrincipalName,
Location,
ResultDescription
| where ResultDescription contains "Access has been blocked due"
| order by UserPrincipalName, NoGBlogins, ResultDescription
| where isnotempty(Location)
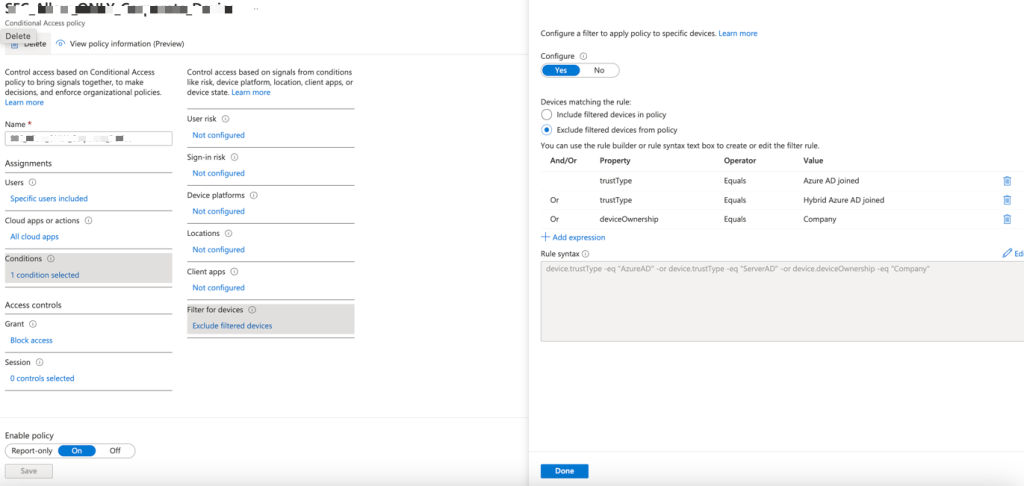
| where isnotempty(ResultDescription)- Step 2 : Create an Azure Security group (To which we will apply a conditional policy that will block Personal Devices) + Conditional Policy—Block Personal Devices. Screenshots have been attached.
In This case, this conditional policy looks for : Azure AD devices, but you can lock it down to Hybrid. This will be based on your environment. You’re looking to apply this security group that sentinel will be filling up to such conditional policy.
Note that : Apple devices may be affected (even if they are corporate). Because they are considered not Azure AD joined.
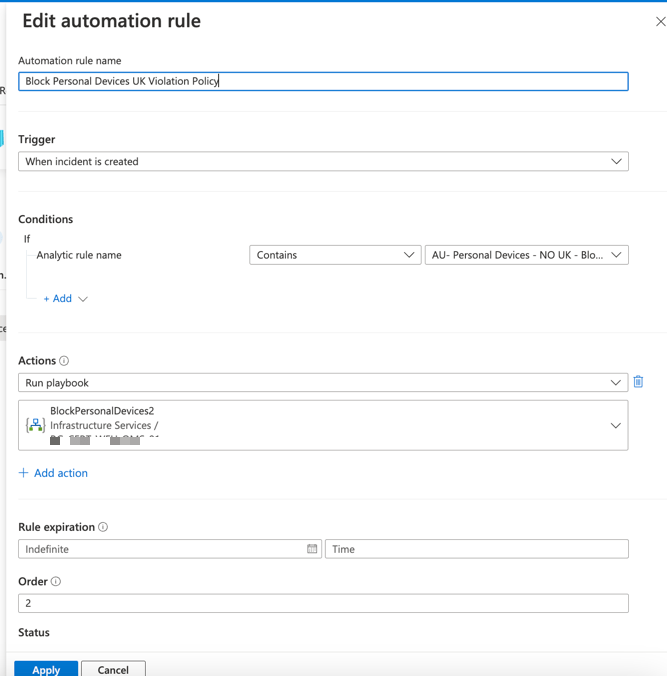
Step 3 : Automation Rule in Sentinel—Logic App on trigger
- Create an automation rule in sentinel to “fill in this security group” of the matches found
- Modify your logic app at your convenience
In this case, the automation rule will run when “Such logins are detected” or it can happen once per day
The idea of the logic app would be the following:
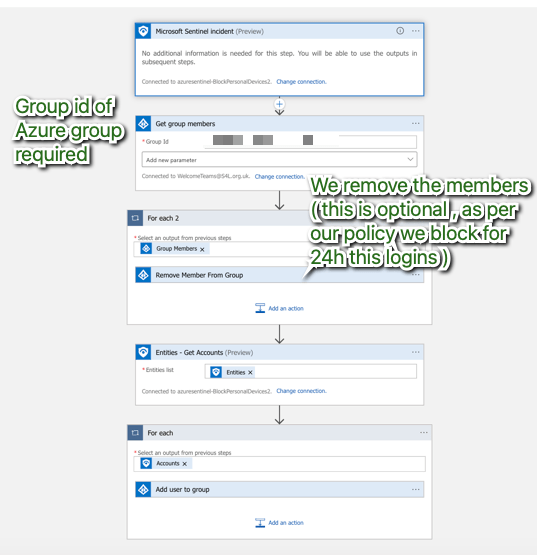
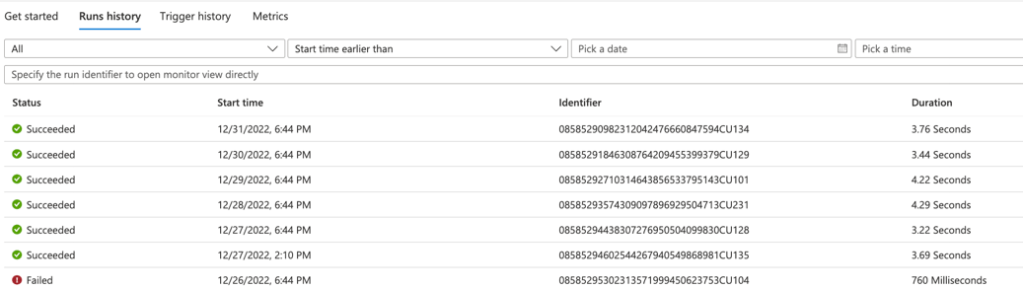
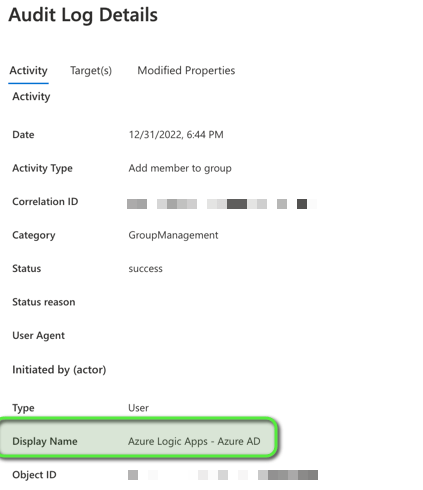
We can see once configured in action the play book adding / removing users in the logic app run history & Group audit logs.