This alert fires when message containing phish was delivered due to an ETR override. ( mail flow rule )
In order to resolve and troubleshoot . We have to get into the exchange mail flow portal and investigate why could potentially a mail flow rule allow phising emails . In the following scenario we have used Sentinel , but you can also use 365 Defender as per the screenshots below
It’s a old and nasty common practice to use mailflow rules in the past to allow certain emails to get in your tenant . Sentinel also monitors for you if Phish is being overrided via Defender
This guide has used Sentinel to get data as the Email ID .
Good Practice is to Review Mail Flow , Spam and any other protections IP ranges & Whitelisting every 6 months and Document each change and why.
Once you Receive the alert , ensure to get the user ( recipient ) & The Internet message id . We will use this to message trace the mail flow rule that is allowing the phish to get in the email.
365 Defender Alert Screenshot + Sentinel



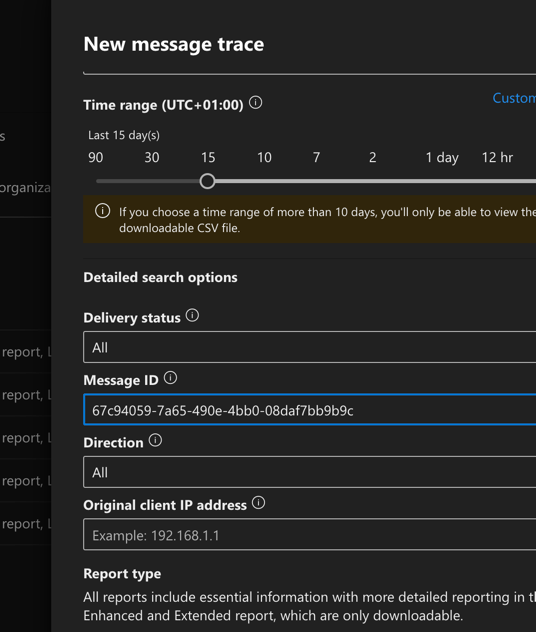
Investigate in Exchange the ETR override using message trace. in Exchange Console, mail flow

In the mail flow properties , fill the data according the entity that the alert is logging & the internet message id that you can get from the alert in the entities section

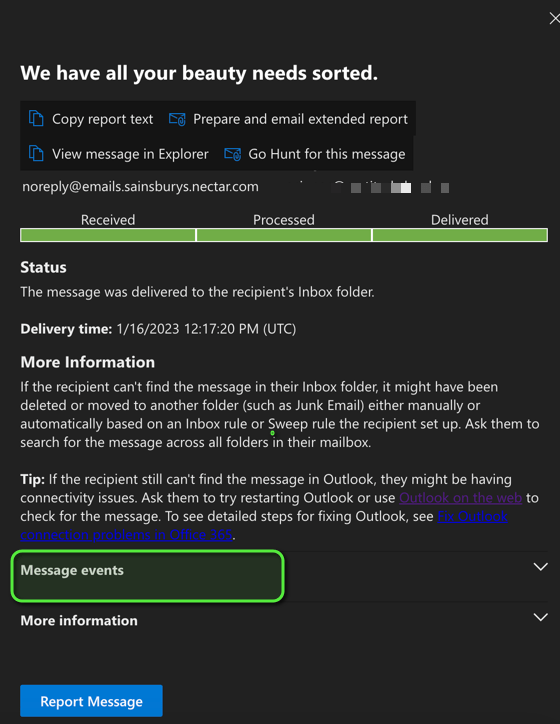

Once the transport rule is identified, you can now safely remove it if necessary on the Mail Flow Rules
